Key Findings from Nokia’s 2020 Threat Intelligence Report

COVID-19 attacks, malware & phishing – Top mobile risks identified in Nokia’s 2020 Threat Intelligence Report
Recently, Nokia released their 2020 Threat Intelligence Report. Their research examined global trends in malware threats across mobile and fixed network traffic from over 150 million devices. This prompted us to compare Nokia’s key mobile malware findings to the threats that we, in Corrata, have been seeing across smartphones and tablets this year.
The Role of COVID-19
COVID-19 has been directly responsible for an increase in mobile malware infections. According to the NCSC Annual Review 2020, one in three cyber attacks in the UK are coronavirus-related. In April alone, Google blocked 18 million daily malware and phishing emails related to coronavirus.
Fear and uncertainty in the early months of the pandemic meant that individuals were more likely to forget safe browsing in a panic for information. Nokia detailed how hackers jumped on the opportunity, disguising phishing sites and ransomware apps as legitimate coronavirus information sources. Reportedly, a whopping nine in ten coronavirus domains are actually a scam.
Cyber criminals went as far as creating a new wiper malware family called CoViper. The malicious software disguised itself as files relating to COVID-19.
Another example included in the report was the ‘Coronavirus Map’ trojan. The map appeared to track outbreaks of the virus across the world. In reality, behind the interactive dashboard, users were unknowingly downloading a password-stealing malware onto their device.

Hackers Target Android
Nokia reports that Android devices were responsible for 26.64% of all infections in 2020 beating Windows/PCs, IoT devices and iPhones. In an effort to eliminate the number of malware attacks, Google Play is continually improving its security and app vetting. So why are Androids so vulnerable? The main reason is because Android users have the capability of sideloading applications from third party app stores. Due to the lack of security and vetting measures on these sites, third party app stores are “rife… with trojanized applications”.
These are the top threats that Nokia and we, at Corrata have identified that we should all be aware of to combat cyber criminals:
- Spyware
- Trojans
- Smishing
Top Threats
(1) Spyware and Info Stealers
Nokia reported that spyware and info stealers attacks have surged this year making up a third of all mobile malware infections. As the names suggest, these types of malware give hackers complete visibility of the device and allows them to harvest user credentials including passwords, phone contacts and photos.
Certain info stealers give hackers remote access to the device allowing them to carry out malicious attacks. With smartphones being used for both personal and business use, a successful spyware infiltration could be detrimental to the financial and reputational costs of a business.
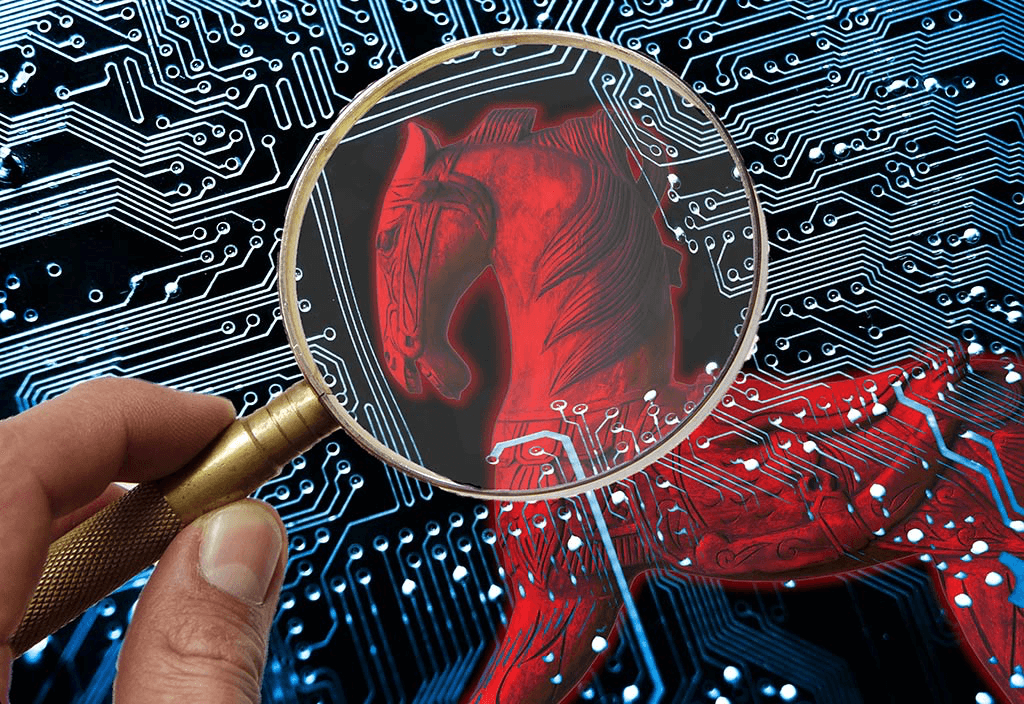
(2) Banking Trojans
According to the report, trojans are the most popular choice of malware for cyber criminals in 2020. This type of malware disguises itself as a legitimate piece of software. However, once downloaded, the trojan can take control of the entire device to steal data or carry out harmful actions on the data or network.
Nokia reported that cyber criminals’ primary motive is to steal user credentials, in particular, banking credentials. One example of a banking trojan was Banker.BR discovered in April 2020 which targeted Spanish and Portuguese speaking countries. Another named BlackRock, was discovered a month later which managed to avoid detection from a number of antivirus solutions.
(3) Smishing
Corrata and our partners at Three Ireland have noticed a huge upsurge in attempted smishing attacks. While we tend to be highly suspicious of an unknown number, an SMS can be configured so that a name pops up on screen instead. This allows hackers to easily impersonate reputable companies such as banks and financial institutions.
There is a sense of urgency associated with these messages. They warn users of suspicious account activity and urge them to take immediate action by clicking on an embedded link to verify their credentials.
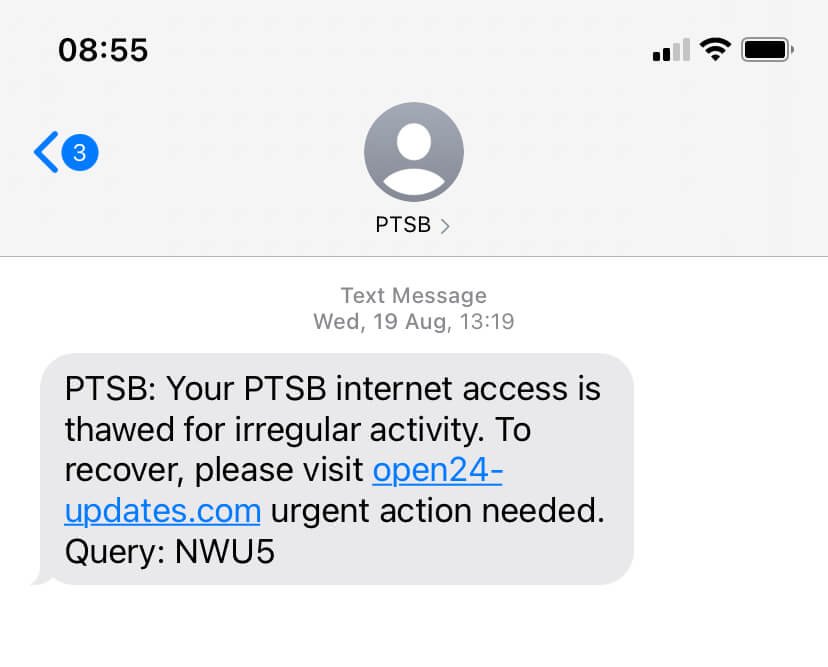
Traditional anti-virus solutions don’t protect against these types of attacks. This means that the targeted employee is the only line of defense against a potential breach. The reality is that the majority of successful data breaches are caused by human error. This is why organizations are increasingly turning to mobile threat defense solutions like Corrata. For example, if an employee accidentally clicked on the dangerous link in the PTSB smishing text above, Corrata would immediately block the URL from opening.
Key Takeaways
Nokia’s research highlights that android devices are the most common malware targets as hackers masquerade malicious software on dodgy third-party app stores. To be safe, Android users should only download applications from reputable sources such as the Google Play Store.
The upsurge in attacks directly associated with COVID-19 reminds us of how cyber criminals take advantage of global trends and real-time events to increase their attack success rate. When seeking coronavirus related information, stick to trusted verified sources such as WHO and government information websites.
Spyware, trojans and smishing are some of the top tactics cyber criminals are using in 2020 to steal mobile user credentials. Smartphone users should be wary of any message or app that requires urgent verification. Most importantly, never click on an attached link. Instead, log in to your account through your browser to double check.
The above findings illustrate how vulnerable smartphones and tablets are to malicious threats without a robust mobile security solution in place. As businesses begin to implement long term remote working strategies, mobile devices are now critical tools for employees. Cyber criminals are acutely aware of this and mobile specific threats will likely only increase in 2021.