Sideloading from Unofficial App Stores – Why Do We Do It?

Is a free app worth the risks?
For most users, installing an app is a simple safe process that involves downloading a file from their app store. However, there is an alternative to the official Apple App Store or Google Play Store which presents serious risks.
‘Sideloading’ is the process of downloading and installing apps onto a mobile device from an unofficial source. On Android, users enable device settings to download apps from unknown sources. On iOS, users had to jail-breaking their device to sideload. More recently, hackers have used fraudulent or stolen enterprise app certificates to distribute unofficial apps. However, many users remain unaware of the potential risks involved in using this technique. In their 2018 Year in Review, Google reported that Android devices that install apps from sources other than Google Play were 8 times more likely to have a Potentially Harmful App (PHA). Also, numerous reports have found trojans, spyware, click fraud and phishing code hidden within unofficial apps. If installed on a mobile, they could pose a serious danger to the security of the device.
So let’s have a closer look at sideloading. How does it work? What are the potential risks? And, despite these risks, why do so many people continue to download their apps from unofficial app stores?
What exactly is sideloading?
Sideloading involves manually downloading and installing an app from an installer file outside of an official app store. There are two distinct ways that users achieve this on Android and iOS devices.
For Android, sideloading used to require the user to simply tick a box in their device settings. This would enable the download of an app .apk file from an ‘unknown source’, i.e. not Google Play Store. Therefore, it’s security feature, Google Play Protect cannot vet the app. Following the release of Android 8 Oreo however, this process has changed dramatically. Now, the user receives a warning every time they wish to sideload an app from an unofficial source. This has the positive effect of preventing apps from installing other apps without the user’s permission. With these settings enabled however, users can download from third party app stores such as Getjar, Mobogenie, SlideME and Appbrain or they can simply search for android .apk files and choose from the legion of available offerings online.
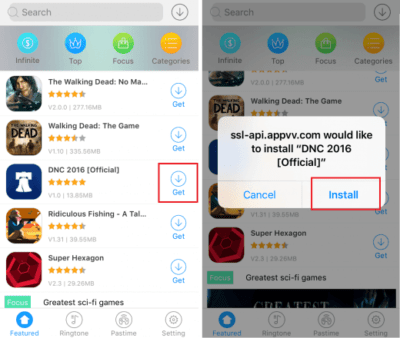
For iOS, there have also been changes to how mobile users access unofficial apps. Reporters revealed that several rogue marketplaces, dubbed ‘DarkSideLoaders’, have made it possible to download millions of apps for non-jailbroken iOS devices. As we previously reported, app developers have discovered a way to use Apple’s Enterprise Developer program to distribute apps outside of the app store. The process involves posing as a legitimate business to obtain an Apple Enterprise App certificate. Earlier this year TechCrunch uncovered more than a dozen hardcore pornography and real-money gambling apps as well as modified versions of popular iOS apps such as Spotify, Angry Birds and Minecraft developed under this program and available for download independent of the App Store.
What are the risks?
Not all third-party app stores and the content they offer may pose a risk to device and data safety. However, it cannot be denied that without regulations or checks, sideloading has its risks. In recent years, countless reports have found hidden threats in unofficial apps. These threats, mainly consist of malware such as Trojans and spyware. Hackers design these threats to inhibit the use of mobile devices and to collect sensitive information.
The App Store and Google Play Store pride themselves in their ability to vet apps before making them public. Google’s Play Protect security feature describes itself as “the most widely deployed mobile threat protection service in the world”, scanning over 50 billion apps across 2 billion devices every day and vetting more than 500k apps per day. In 2018, Google found that 0.68% of devices that installed apps from outside the Google Play Store were affected by one or more PHAs, while the PHA install rate for apps inside the official store was only 0.04%.
Similarly, since the release of the App Store in 2008, Apple has sought to differentiate the iPhone as robust. By distributing via unofficial third-party marketplaces, apps can access operating functions that App Store and Google Play Store would normally ban. Circumventing their strict policies means that hackers can use unofficial apps to install malware or phishing software. On Android, there have been numerous reports of sideloaded apps attempting to root devices, installing apps without user permission, and communicating to known malicious sites online. On iOS, unofficial apps have been used as Remote Access Trojans, allowing attackers to gain access to mobile devices of employees while active on internal corporate networks, putting both personal and corporate sensitive data at risk.
So why do people use unofficial app stores?
We have found that there are three main reasons:
It’s free
The biggest reason seems to be a simple one: users want to download content without paying for it. Many of these third-party marketplaces offer games and wallpapers for free. Children particularly find this type of content attractive. When it was discovered in 2015, the unofficial marketplace vShare offered all of the top ten paid apps on the App Store for free, including well-known titles such as Grand Theft Auto and Clash of Clans, while alternative versions of apps such as Spotify and Pokemon Go, offering the same services without the regular ads or fees, were discovered earlier this year. Unofficial apps can also give users access to free streamed content such as movies, TV shows, and music.
Location Restrictions
Users may also turn to unofficial app stores to get around geographical restrictions of content. Often, developers only release apps or other media to select regions initially. This means that people living in other locations must wait months to access the content. For example when events like Game of Thrones’ final season or the release of Marvel’s Avengers: Endgame earlier this year made it extremely important for people to access content as it was released to avoid spoilers and stay up-to-date with the latest cultural phenomena.
It’s the only option
The third reason is simply that it is the only way that users can access the content. In 2018, Fortnite, the hugely popular online video game announced that it would be made available for download to Android devices but with a catch. Instead of downloading via Google Play Store, users would need to sideload the game’s .apk file from developer Epic Games’ website. In situations like this, users potentially leave themselves vulnerable to compromise.

Source: Epic Games
As enterprise mobility increases and over 80% of worker tasks are expected to take place on mobile by 2021, it is crucial that every employee device and the data it accesses is secured. But with the increased use of sideloading and so many of us using our mobile devices for personal as well as professional business, it is easy to see how a seemingly simple act like downloading a free version of a game or streaming the latest episode of our favorite TV show could have serious consequences for the safety of our personal as well as corporate data. Corrata can help secure mobile devices from threats arising from third-party app downloads. Learn more about our easy security app.
For more industry news, insights and analysis – follow us on LinkedIn!




