Cloud App Discovery in a mobile first world

With the growing popularity of SaaS services, sticking to the safe zone is key.
The rapid adoption of 3rd party SaaS services has driven cloud computing and digital transformation for many organizations. Google Drive, Dropbox and Salesforce amongst many others spring to mind. Services based on the SaaS model offer fantastic advantages.
For a start, they do not require in-house infrastructure. As well as that, they have rich out of the box features sets and delivery across both web and mobile platforms. Also, they have low upfront commitment and automatic version updates. Their advantages are endless…
Saas challenges
However, SaaS applications do present security challenges. In particular, corporate data can easily slip beyond the control of the company’s ‘gatekeeper’. Once your CRM is in the cloud, your visibility is limited.
Imagine that a soon to depart salesperson has downloaded the contact details of your entire customer base. Without taking appropriate steps, you would have no idea. Or, imagine that important IP diagrams have been accessed repeatedly by someone in the post room.
What makes this problem particularly difficult for InfoSec teams is a parallel development. Not only are your apps leaving the data-centre, but your employees are leaving the building. In the good old days, you might have used Firewalls and Proxies to give you visibility and control over app usage.
But with employees working from home, airports and coffee shops, the network perimeter has disappeared. In this new world, how can you have any idea what’s going on, let alone impose control?
The endpoint is key
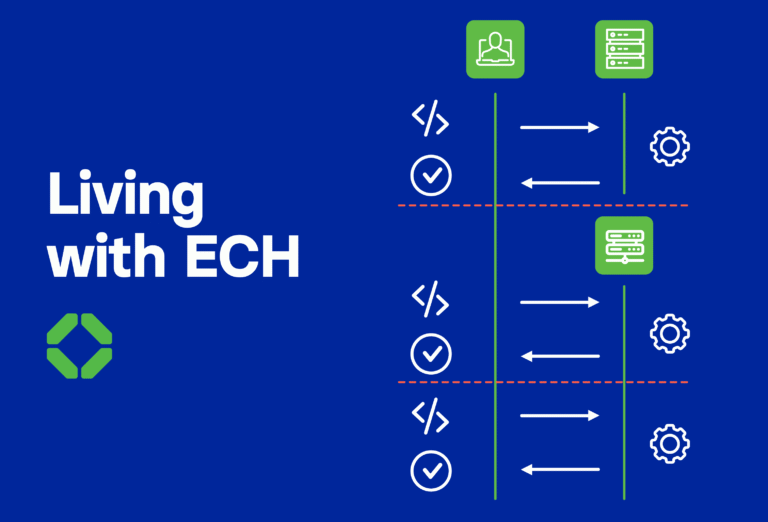
The answer is what the industry calls “endpoint cloud application discovery and control”. What does this clunky phrase refer to, you ask? In a world where the corporate perimeter has disappeared, the endpoint is the key.
Initially, cloud app discovery and control relied on network firewalls and proxies. Now, the focus is switching the point of discovery and control to the endpoint (laptop, mobile, desktop).
At Ignite 2019, Microsoft announced endpoint based cloud discovery on Windows. But, what about the vast numbers of mobile devices running iOS and Android?
Visibility and control
That’s where Corrata comes in. Corrata extends endpoint based cloud app discovery and control to phones and tablets. So, now you can detect in real time those employees who are putting your organization at risk. Maybe they are using unsanctioned cloud storage apps for uploading client data or using unapproved marketing automation tools.
But more importantly, with Corrata, you can also block access to risky apps. Corrata prevents employee mobile devices connecting to cloud services. And not only that, Corrata will do this regardless of whether the service is accessed via a browser or a native app. So, as your business embraces SaaS services, with Corrata onboard you can be confident that your employees stick to the safe zone.