key Technology Partner
Microsoft
Enhanced Endpoint Security & Experience

Corrata integrates with a range of Microsoft products including Intune and Defender for Endpoint to create unique capabilities and simplify deployment and management for our joint customers. Corrata is a member of the Microsoft Intelligent Security Alliance.
Microsoft Defender for Endpoint
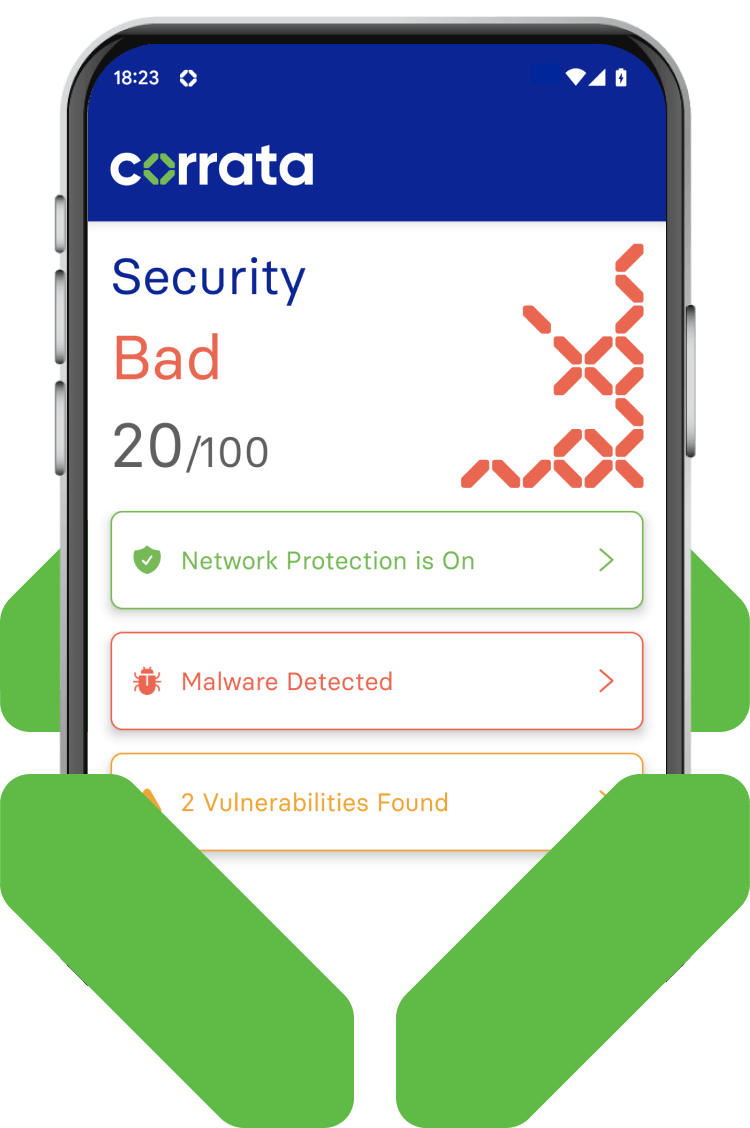
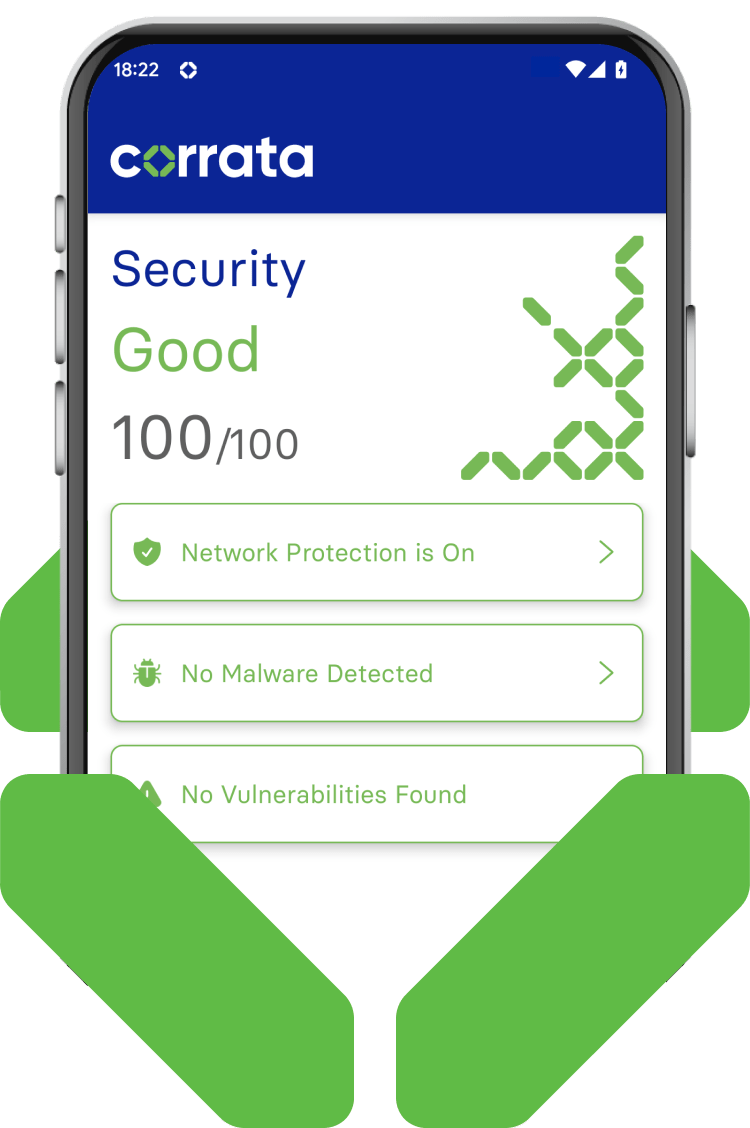
Together the two solutions provide an integrated view of an organization’s and a user’s threat status and improve the speed, productivity and effectiveness of threat management.
- Corrata’s integration with Microsoft Defender for Endpoint enables Microsoft customers to detect, protect and respond to security threats on iOS and Android devices.
- Corporate IT teams get a ‘single pane of glass' for all device platforms to investigate and defend against any potential threats.
- Microsoft Defender for Endpoint users can investigate mobile security threats directly from within the Microsoft Defender Security Center.
Microsoft Cloud App Security
- Mobile Devices
The collaboration with Microsoft Cloud App Security (MCAS) brings together Corrata’s unique capability for collecting traffic information and controlling app usage on mobile devices with Microsoft’s market-leading Cloud Access Security Broker (CASB).
Traffic information from smartphones and tablets running Corrata is uploaded for analysis to Microsoft Cloud App Security on a continuous basis.
- Usage information
Cloud app usage information collected by Corrata is visible to admins via the Microsoft Cloud App Security console. This provides an integrated view of an organization’s cloud app usage and one-click enforcement of app usage policies across iOS, Android, and Windows devices.
Once apps are designated as risky or un-sanctioned within the MCAS portal they will automatically be blocked by Corrata on the mobile endpoint. This capability is delivered using Corrata’s patented SafePathML technology which powers the world’s only enterprise-grade firewall for mobile devices.
